HTB: Conversor Machine Walkthrougs
HTB Conversor Machine Walkthrougs
Please you planning challenge for yourself. This is Walkthrougs is not for copy, only researcher document
Reconnaissance
This section details the reconnaissance activities performed on the target system. We must slowly and only recon with tactical analysis.
Host Resolution
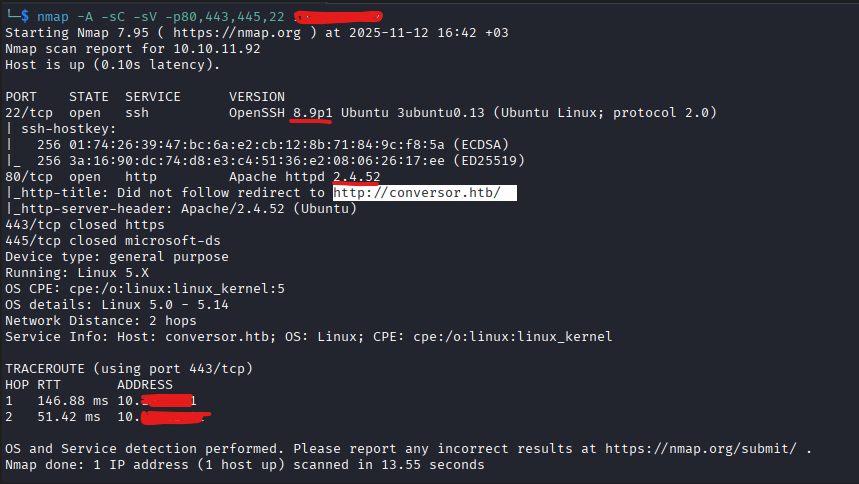
nmap -A -sC -sV -p80,443,445,22 10.XX.XX.XX
Nmap scan all port
Let scan pipe bash under to backround with nohup.
nohup nmap -sS -sC -sV -p- conversor.htb -oN nmap.txt -vvv &If I want to see the instant output of the scan results, I can run this command whenever I want. This provides a clean workspace and the ability to use only one terminal.
cat nohup.out | grep Discovered
Discovered open port 22/tcp on 10.XX.XX.XX
Discovered open port 80/tcp on 10.XX.XX.XX# Nmap 7.95 scan initiated Wed Nov 12 16:59:10 2025 as: /usr/lib/nmap/nmap --privileged -sS -sC -sV -p- -oN nmap.txt -vvv conversor.htb
Nmap scan report for conversor.htb (10.XX.XX.XX)
Host is up, received echo-reply ttl 63 (0.14s latency).
Scanned at 2025-11-12 16:59:10 +03 for 388s
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 8.9p1 Ubuntu 3ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 01:74:26:39:47:bc:6a:e2:cb:12:8b:71:84:9c:f8:5a (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBJ9JqBn+xSQHg4I+jiEo+FiiRUhIRrVFyvZWz1pynUb/txOEximgV3lqjMSYxeV/9hieOFZewt/ACQbPhbR/oaE=
| 256 3a:16:90:dc:74:d8:e3:c4:51:36:e2:08:06:26:17:ee (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIIR1sFcTPihpLp0OemLScFRf8nSrybmPGzOs83oKikw+
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.52
|_http-server-header: Apache/2.4.52 (Ubuntu)
| http-title: Login
|_Requested resource was /login
| http-methods:
|_ Supported Methods: OPTIONS GET HEAD
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Wed Nov 12 17:05:38 2025 -- 1 IP address (1 host up) scanned in 388.06 secondsWell anyway, time for step 2 at the Recon.
We are now performing directory analysis with ffuf. However, we need to check the analysis with network bandwidth and response time. So this is issue developed small script with python. and analyzed
python3 main.py --url http://conversor.htb
*** ffuf -t tester (please use only permitted purposes) ***
target URL: http://conversor.htb
target for request by URL: http://conversor.htb
Host header to be sent: (absent)
[1/8] status=200 time=0.540s size=722
[2/8] status=200 time=0.614s size=722
[3/8] status=200 time=0.535s size=722
[4/8] status=200 time=0.530s size=722
[5/8] status=200 time=0.480s size=722
[6/8] status=200 time=0.533s size=722
[7/8] status=200 time=0.644s size=722
[8/8] status=200 time=0.524s size=722
--- summary (bybiyik) ---
Avarage response time: 0.550 s (medyan 0.534 s, stdev 0.049)
Avarage response size: 722 bytes
--- Hesaplama ---
Target RPS: 30.0 req/s
basic t = RPS * avg_response_time = 30.0 * 0.550 = 16.50
Security factory (50%) applied: t_adjusted = 24.75
approximately t (integer): 25
estimated bandwidth requirement: 31.73 KB/s
done.let use -t 25 count.
ffuf -w /usr/share/seclists/Discovery/Web-Content/raft-large-directories-lowercase.txt -u http://conversor.htb/FUZZ -e .php,.html,.txt,.js,.json,.xml,.bak,.old -fc 404,403 -t 25 -o ffuf.txt
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://conversor.htb/FUZZ
:: Wordlist : FUZZ: /usr/share/seclists/Discovery/Web-Content/raft-large-directories-lowercase.txt
:: Extensions : .php .html .txt .js .json .xml .bak .old
:: Output file : ffuf.txt
:: File format : json
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 25
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
:: Filter : Response status: 404,403
________________________________________________
logout [Status: 302, Size: 199, Words: 18, Lines: 6, Duration: 59ms]
register [Status: 200, Size: 726, Words: 30, Lines: 21, Duration: 61ms]
login [Status: 200, Size: 722, Words: 30, Lines: 22, Duration: 65ms]
about [Status: 200, Size: 2842, Words: 577, Lines: 81, Duration: 82ms]
javascript [Status: 301, Size: 319, Words: 20, Lines: 10, Duration: 56ms]
convert [Status: 405, Size: 153, Words: 16, Lines: 6, Duration: 101ms]
:: Progress: [505458/505458] :: Job [1/1] :: 326 req/sec :: Duration: [0:23:34] :: Errors: 0 ::